We may not have the course you’re looking for. If you enquire or give us a call on 01344203999 and speak to our training experts, we may still be able to help with your training requirements.

close
Press esc to close

close


Press esc to close

close
Fill out your contact details below and our training experts will be in touch.



Back to Course Information
Module 1: Introduction to Microsoft 365 Threat Protection
Module 2: Mitigate Incidents Using Microsoft 365 Defender
Module 3: Protect Your Identities with Azure AD Identity Protection
Module 4: Remediate Risks with Microsoft Defender for Office 365
Module 5: Safeguard Your Environment with Microsoft Defender for Identity
Module 6: Secure Your Cloud Apps and Services with Microsoft Defender for Cloud Apps
Module 7: Respond to Data Loss Prevention Alerts Using Microsoft 365
Module 8: Manage Insider Risk in Microsoft Purview
Module 9: Investigate Threats by Using Audit Features in Microsoft 365 Defender and Microsoft Purview Standard
Module 10: Investigate Threats Using Audit in Microsoft 365 Defender and Microsoft Purview (Premium)
Module 11: Investigate Threats with Content Search in Microsoft Purview
Module 12: Protect Against Threats with Microsoft Defender for Endpoint
Module 13: Deploy the Microsoft Defender for Endpoint Environment
Module 14: Implement Windows Security Enhancements with Microsoft Defender for Endpoint
Module 15: Perform Device Investigations in Microsoft Defender for Endpoint
Module 16: Perform Actions on a Device Using Microsoft Defender for Endpoint
Module 17: Perform Evidence and Entities Investigations Using Microsoft Defender for Endpoint
Module 18: Configure and Manage Automation Using Microsoft Defender for Endpoint
Module 19: Configure for Alerts and Detections in Microsoft Defender for Endpoint
Module 20: Utilise Vulnerability Management in Microsoft Defender for Endpoint
Module 21: Plan for Cloud Workload Protections Using Microsoft Defender for Cloud
Module 22: Connect Azure Assets to Microsoft Defender for Cloud
Module 23: Connect Non-Azure Resources to Microsoft Defender for Cloud
Module 24: Manage Your Cloud Security Posture Management
Module 25: Explain Cloud Workload Protections in Microsoft Defender for Cloud
Module 26: Remediate Security Alerts Using Microsoft Defender for Cloud
Module 27: Construct KQL Statements for Microsoft Sentinel
Module 28: Analyse Query Results Using KQL
Module 29: Build Multi-Table Statements Using KQL
Module 30: Work with Data in Microsoft Sentinel Using Kusto Query Language
Module 31: Introduction to Microsoft Sentinel
Module 32: Create and Manage Microsoft Sentinel Workspaces
Module 33: Query Logs in Microsoft Sentinel
Module 34: Use Watchlists in Microsoft Sentinel
Module 35: Utilise Threat Intelligence in Microsoft Sentinel
Module 36: Connect Data to Microsoft Sentinel Using Data Connectors
Module 37: Connect Microsoft Services to Microsoft Sentinel
Module 38: Connect Microsoft 365 Defender to Microsoft Sentinel
Module 39: Connect Windows Hosts to Microsoft Sentinel
Module 40: Connect Common Event Format Logs to Microsoft Sentinel
Module 41: Connect Syslog Data Sources to Microsoft Sentinel
Module 42: Connect Threat Indicators to Microsoft Sentinel
Module 43: Threat Detection with Microsoft Sentinel Analytics
Module 44: Automation in Microsoft Sentinel
Module 45: Security Incident Management in Microsoft Sentinel
Module 46: Identify Threats with Behavioral Analytics
Module 47: Data Normalisation in Microsoft Sentinel
Module 48: Query, Visualise, and Monitor Data in Microsoft Sentinel
Module 49: Manage Content in Microsoft Sentinel
Module 50: Explain Threat Hunting Concepts in Microsoft Sentinel
Module 51: Threat Hunting with Microsoft Sentinel
Module 52: Use Search Jobs in Microsoft Sentinel
Module 53: Hunt for Threats Using Notebooks in Microsoft Sentinel


This Microsoft Security Operations Analyst SC200 Course is designed for individuals who are interested in developing their skills and expertise in the field of Security Operations and Threat Detection and Response using Microsoft technologies. This training course is especially beneficial for the following professionals:
There are no formal prerequisites for this Microsoft Security Operations Analyst SC200 Course. However, basic knowledge of Cybersecurity and IT concepts would be beneficial for the delegates.
The Microsoft Security Operations Analyst SC200 Training is a vital course that equips professionals with the knowledge and skills needed to investigate, respond to, and hunt for threats using Microsoft Sentinel, Microsoft Defender for Cloud, and Microsoft 365 Defender. In today's cybersecurity landscape, the ability to mitigate cyberthreats is of utmost importance, making this course highly relevant and valuable.
Professionals involved in Security Operations roles, including Security Engineers, Analysts, and those responsible for safeguarding digital assets, should aim to master this subject. With the increasing sophistication of cyber threats, knowing how to effectively use these technologies and Kusto Query Language (KQL) is crucial for ensuring the security and resilience of an organisation's digital infrastructure.
The 4-day training course offered by the Knowledge Academy is designed to empower delegates with the practical skills and knowledge necessary to excel in a Security Operations job role. This course focuses on configuring and using Microsoft Sentinel and utilising KQL for detection, analysis, and reporting. It also prepares learners for the SC-200: Microsoft Security Operations Analyst exam, making it a comprehensive and valuable training opportunity.
Course Objectives:
Upon completion of this Microsoft Security Engineer Training Course, delegates will benefit from an advanced skill set and in-depth knowledge of threat mitigation using Microsoft security technologies. They will be well-prepared to effectively respond to cyber threats, enhancing their organisation's security posture and contributing to a safer digital environment.




Why choose us
Our easy to use Virtual platform allows you to sit the course from home with a live instructor. You will follow the same schedule as the classroom course, and will be able to interact with the trainer and other delegates.


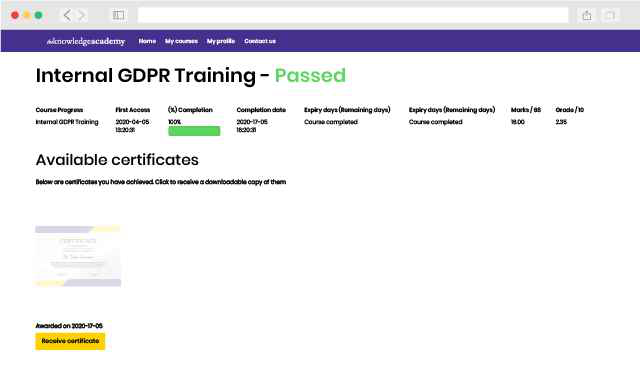
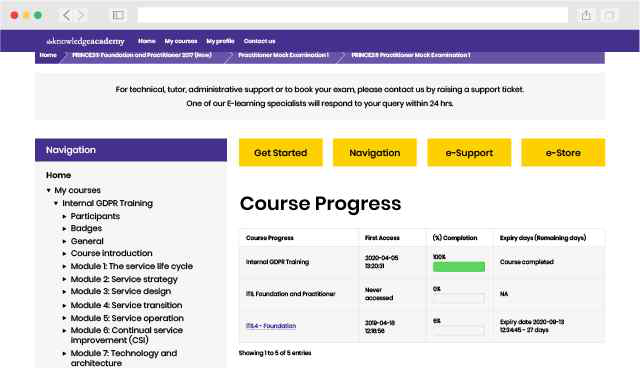
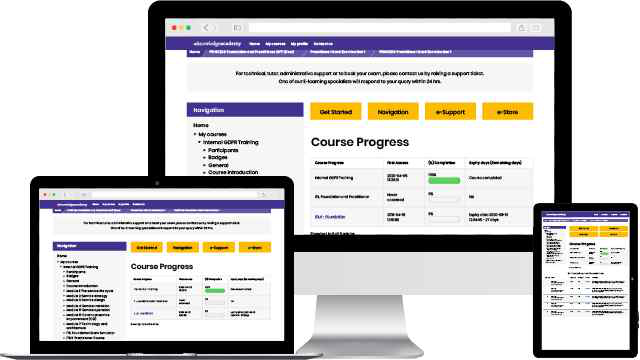
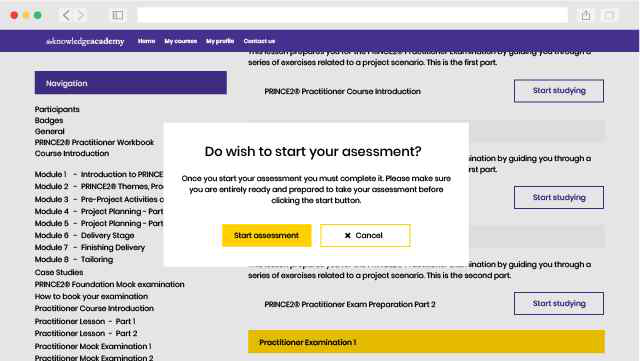
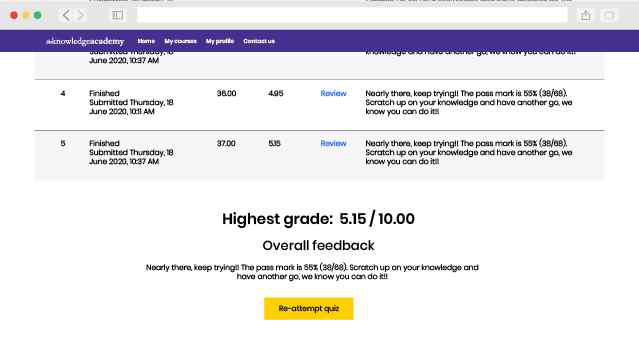
Our fully interactive online training platform is compatible across all devices and can be accessed from anywhere, at any time. All our online courses come with a standard 90 days access that can be extended upon request. Our expert trainers are constantly on hand to help you with any questions which may arise.
This is our most popular style of learning. We run courses in 1200 locations, across 200 countries in one of our hand-picked training venues, providing the all important ‘human touch’ which may be missed in other learning styles.

All our trainers are highly qualified, have 10+ years of real-world experience and will provide you with an engaging learning experience.

We only use the highest standard of learning facilities to make sure your experience is as comfortable and distraction-free as possible

We limit our class sizes to promote better discussion and ensuring everyone has a personalized experience

Get more bang for your buck! If you find your chosen course cheaper elsewhere, we’ll match it!
This is the same great training as our classroom learning but carried out at your own business premises. This is the perfect option for larger scale training requirements and means less time away from the office.

Our courses can be adapted to meet your individual project or business requirements regardless of scope.

Cut unnecessary costs and focus your entire budget on what really matters, the training.

This gives your team a great opportunity to come together, bond, and discuss, which you may not get in a standard classroom setting.

Keep track of your employees’ progression and performance in your own workspace.
Asim was punctual, interested, engaging and patient. An excellent experience.
You won't find better value in the marketplace. If you do find a lower price, we will beat it.

Flexible delivery methods are available depending on your learning style.
Resources are included for a comprehensive learning experience.




"Really good course and well organised. Trainer was great with a sense of humour - his experience allowed a free flowing course, structured to help you gain as much information & relevant experience whilst helping prepare you for the exam"
Joshua Davies, Thames Water



 Back to course information
Back to course information
We may not have any package deals available including this course. If you enquire or give us a call on 01344203999 and speak to our training experts, we should be able to help you with your requirements.
 If you miss out, enquire to get yourself on the waiting list for the next day!
If you miss out, enquire to get yourself on the waiting list for the next day!