We may not have the course you’re looking for. If you enquire or give us a call on 01344203999 and speak to our training experts, we may still be able to help with your training requirements.

close
Press esc to close

close


Press esc to close

close
Fill out your contact details below and our training experts will be in touch.



Back to Course Information
Module 1: Introduction to Zero Trust and Best Practice Frameworks
Module 2: Design Solutions that Align with the Cloud Adoption Framework (CAF) and Well-Architected Framework (WAF)
Module 3: Design Solutions that Align with the Microsoft Cybersecurity Reference Architecture (MCRA) and Microsoft Cloud Security Benchmark (MCSB)
Module 4: Design a Resiliency Strategy for Common Cyberthreats Like Ransomware
Module 5: Case study: Design solutions that align with security best practices and priorities
Module 6: Design Solutions for Regulatory Compliance
Module 7: Design Solutions for Identity and Access Management
Module 8: Design Solutions for Securing Privileged Access
Module 9: Design Solutions for Security Operations
Module 10: Case study: Design Security Operations, Identity and Compliance Capabilities
Module 11: Design Solutions for Securing Microsoft 365
Module 12: Design solutions for Securing Applications
Module 13: Design Solutions for Securing an Organisation's Data
Module 14: Case study: Design Security Solutions for Applications and Data
Module 15: Specify Requirements for Securing SaaS, PaaS, and IaaS Services
Module 16: Design Solutions for Security Posture Management in Hybrid and Multicloud Environments
Module 17: Design Solutions for Securing Server and Client Endpoints
Module 18: Design Solutions for Network Security
Module 19: Case Study: Design Security Solutions for Infrastructure


This Microsoft Cybersecurity Architect SC100 Course is beneficial for those who want to gain an in-depth understanding of Microsoft's Cybersecurity Solutions, especially for Microsoft 365 and Azure services. The professionals who will benefit from this course are:
There are no formal prerequisites for attending this Microsoft Cybersecurity Architect SC100 Training. However, The SC-100 exam is an advanced, expert-level exam that covers a wide range of cybersecurity topics, so advanced experience and knowledge in identity and access, platform protection, security operations, securing data and securing applications is recommended.
The Microsoft Cybersecurity Architect SC100 Course is a comprehensive training that equips professionals with the knowledge to design and evaluate cybersecurity strategies in crucial areas such as Zero Trust, Governance Risk Compliance (GRC), Security Operations (SecOps), and data and applications. In today's increasingly digital world, cybersecurity is of paramount importance, making this a highly relevant course.
Understanding the Microsoft Cybersecurity Architect SC100 is essential for professionals aiming to become proficient in security strategy design and evaluation. Security experts, IT professionals, system architects, and anyone involved in safeguarding critical data and infrastructure should strive to master this subject. By doing so, they can contribute to their organisation's resilience against cyber threats and stay ahead in the field of cybersecurity.
The 4-day training offered by the Knowledge Academy is designed to provide delegates with a comprehensive understanding of the Microsoft Cybersecurity Architect SC100. This course empowers participants to design a Zero Trust strategy and architecture, evaluate GRC technical strategies and security operations, design security for infrastructure, and create a strategy for data and applications.
Course Objectives:
Upon completion of this Microsoft Security Engineer Training Course, delegates will benefit from an enhanced skill set and a thorough understanding of cybersecurity strategies. They will be well-equipped to design and evaluate security solutions, ensuring the protection of their organisation's digital assets and contributing to its overall resilience against cyber threats.




Why choose us
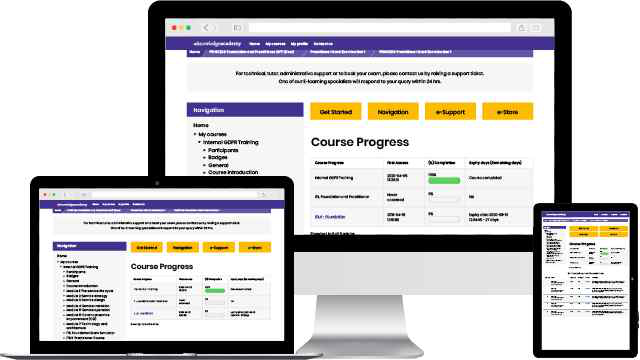
Our easy to use Virtual platform allows you to sit the course from home with a live instructor. You will follow the same schedule as the classroom course, and will be able to interact with the trainer and other delegates.


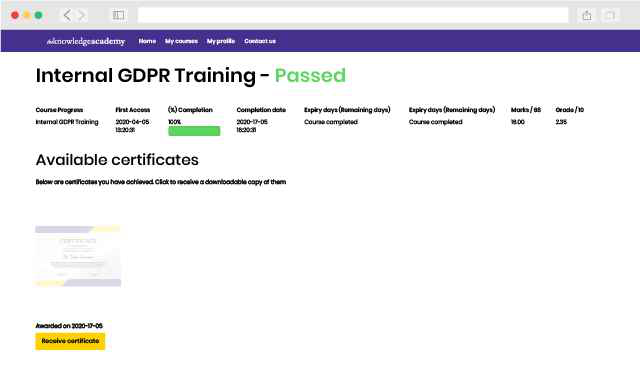
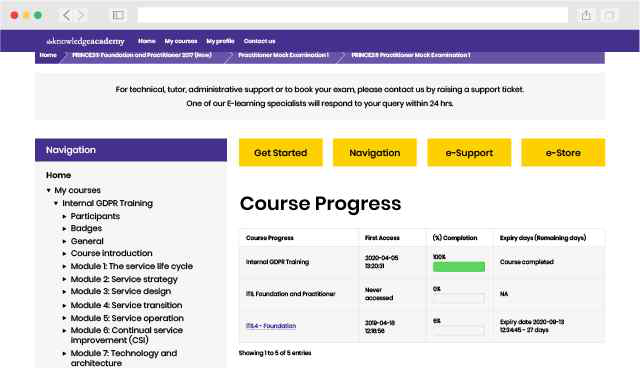
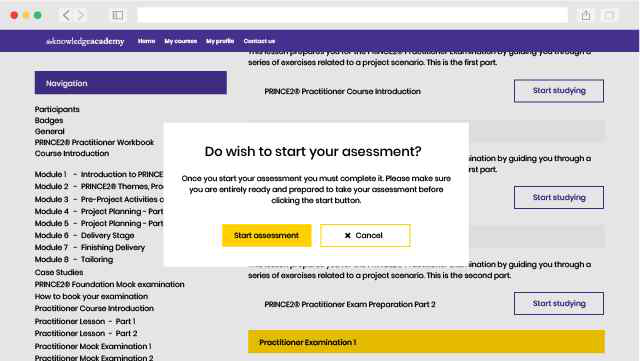
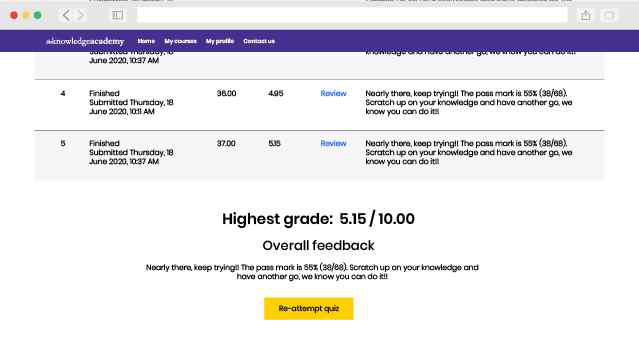
Our fully interactive online training platform is compatible across all devices and can be accessed from anywhere, at any time. All our online courses come with a standard 90 days access that can be extended upon request. Our expert trainers are constantly on hand to help you with any questions which may arise.
This is our most popular style of learning. We run courses in 1200 locations, across 200 countries in one of our hand-picked training venues, providing the all important ‘human touch’ which may be missed in other learning styles.

All our trainers are highly qualified, have 10+ years of real-world experience and will provide you with an engaging learning experience.

We only use the highest standard of learning facilities to make sure your experience is as comfortable and distraction-free as possible

We limit our class sizes to promote better discussion and ensuring everyone has a personalized experience

Get more bang for your buck! If you find your chosen course cheaper elsewhere, we’ll match it!
This is the same great training as our classroom learning but carried out at your own business premises. This is the perfect option for larger scale training requirements and means less time away from the office.

Our courses can be adapted to meet your individual project or business requirements regardless of scope.

Cut unnecessary costs and focus your entire budget on what really matters, the training.

This gives your team a great opportunity to come together, bond, and discuss, which you may not get in a standard classroom setting.

Keep track of your employees’ progression and performance in your own workspace.
You won't find better value in the marketplace. If you do find a lower price, we will beat it.

Flexible delivery methods are available depending on your learning style.
Resources are included for a comprehensive learning experience.




"Really good course and well organised. Trainer was great with a sense of humour - his experience allowed a free flowing course, structured to help you gain as much information & relevant experience whilst helping prepare you for the exam"
Joshua Davies, Thames Water



 Back to course information
Back to course information
We may not have any package deals available including this course. If you enquire or give us a call on 01344203999 and speak to our training experts, we should be able to help you with your requirements.
 If you miss out, enquire to get yourself on the waiting list for the next day!
If you miss out, enquire to get yourself on the waiting list for the next day!